SYS.01 // ENTRY. Why are you still relying on 1995-era SSH protocols to secure 2026-era autonomous intelligence? Standard remote coding configurations currently leak metadata across 85% of existing AI orchestration platforms, creating a massive surface area for credential theft. You know that traditional server setups are too brittle for high-velocity agentic workflows. They're slow, they're loud, and they log everything.
This technical analysis details the protocols, security requirements, and switchboard architectures necessary for secure remote code execution. We'll build a minimalist, zero-log infrastructure that enables seamless interoperability between local AI agents and remote environments. You'll learn to implement an ephemeral runtime state that prioritizes functional utility over durable conversation storage. We're moving away from heavy frameworks toward a lean, un-opinionated orchestration layer that respects your privacy. We'll examine the relay broker mechanics and the common denominator protocols that ensure your agents remain autonomous. It's time to stop building surveillance products and start engineering secure, quiet systems.
Key Takeaways
- Map the evolution of the 2026 stack, shifting from manual interfaces to automated, agent-aware orchestration layers.
- Engineer secure remote coding environments by implementing zero-log architectures that eliminate durable command storage.
- Contrast traditional SSH tunneling with high-efficiency agent switchboards to optimize latency and system orchestration.
- Execute a clinical deployment workflow to provision clean remote nodes and configure them for seamless agentic interoperability.
- Integrate the A2A Linker as a neutral, ephemeral relay broker to maintain privacy across complex agent-to-agent networks.
SYS.01 // Defining the Remote Coding Stack for 2026
Remote coding is the architectural decoupling of the developer interface from the execution environment. In 2026, this definition expands beyond simple screen sharing or basic terminal emulation. Modern infrastructure requires a sophisticated, agent-aware orchestration layer. Traditional tools like RDP or standard SSH sessions lack the granularity needed for autonomous workflows. They fail because they treat the remote session as a monolithic stream of pixels or characters rather than a structured data exchange. This shift demands a move toward environments that understand the underlying system state.
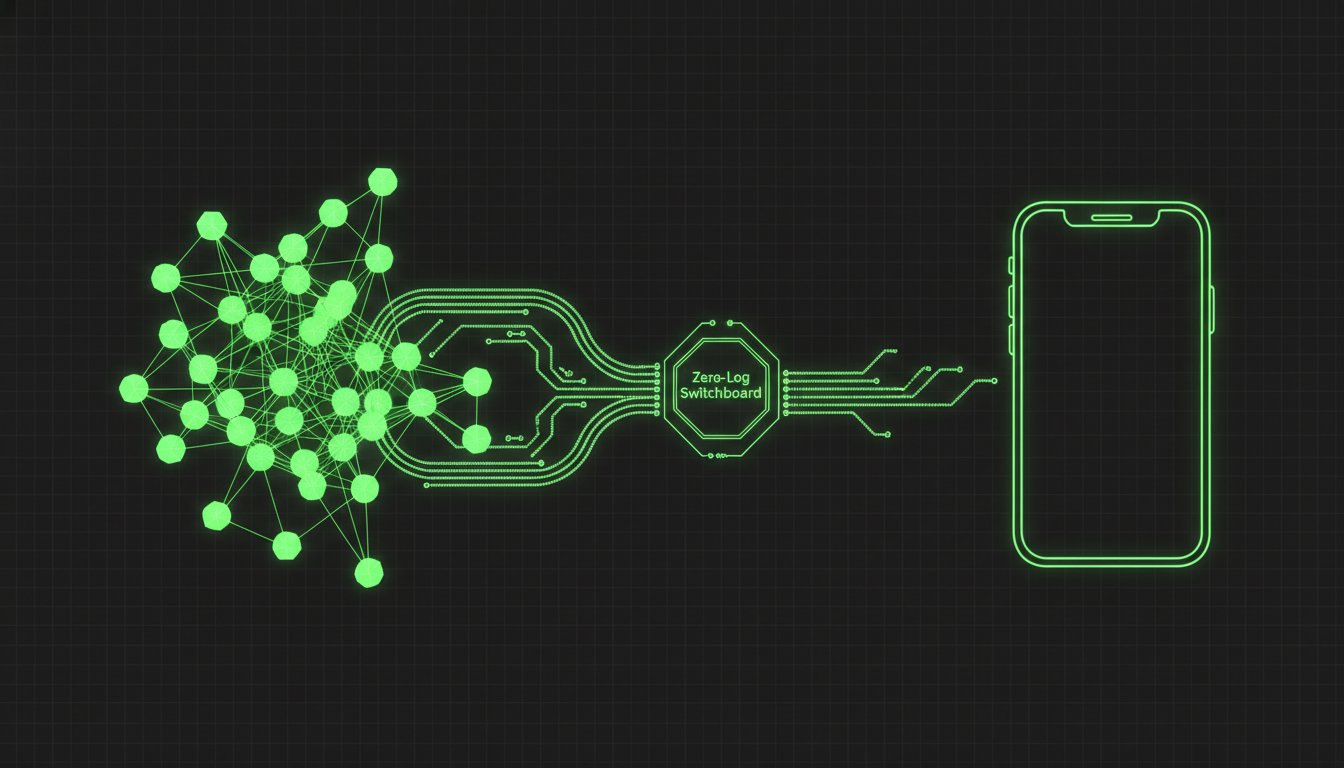
The 2026 stack consists of three core components: the terminal interface, the relay broker, and the remote runtime. The terminal interface acts as the local control plane. The relay broker manages the secure, low-latency handoff of instructions. The remote runtime provides the isolated environment where code actually executes. Many legacy remote tools prioritize surveillance-heavy features like constant session recording and keystroke logging. These features introduce unacceptable privacy risks for high-stakes engineering. A2A Linker prioritizes functional utility over persistent data collection. You can inspect the implementation details at https://github.com/Fu-Rabi/a2alinker.
The Evolution of Remote Execution Protocols
Secure access began with Telnet in 1969, eventually giving way to the encrypted standards of SSH in 1995. However, SSH was designed for human operators. 2026 demands protocols that support machine-to-machine reasoning. This evolution relies heavily on the foundational logic of a Remote Procedure Call (RPC) to facilitate seamless execution across distributed nodes. The emergence of the Model Context Protocol (MCP) marks a shift toward standardized agent-environment interaction. Security now dictates the use of ephemeral runtime states. These environments exist only for the duration of a specific task; they vanish upon completion, leaving no permanent footprint for attackers to exploit.
The Role of AI Agents in Remote Coding
Autonomous agents like Claude Code require direct, high-velocity access to remote file systems. They don't just write code. They inspect directory structures, reason about dependencies, and execute test suites. This creates a need for a common denominator in cross-machine communication. Distributed environments often struggle with agentic handoffs. When an agent moves from a staging server to a production container, state consistency is critical. Systems must handle these transitions without introducing latency or security holes. Efficiency is the only metric that matters. Agents united through a lean relay broker can operate at a scale impossible for human-centric interfaces.
SYS.02 // Architectural Requirements for Secure Remote Access
Secure remote coding hinges on the total elimination of durable state. Traditional architectures fail because they prioritize conversation history over architectural privacy. In a secure agent environment, the system must treat every command as a transient event. Zero-log architecture ensures that no durable conversation or command storage exists on the relay broker. This prevents the accumulation of sensitive intellectual property in third-party databases, reducing the risk of data harvesting. Every interaction is a point-to-point transmission that expires the moment the execution cycle completes.
Encryption must be absolute. Terminal-to-server data streams require end-to-end encryption using TLS 1.3 protocols. This architecture minimizes the attack surface by stripping away unnecessary model API settings that often lead to unauthorized privilege escalation. If a feature is not required for the immediate task, it remains disabled in the runtime environment. The orchestration layer functions as a neutral switchboard. It manages multiple agent connections without inspecting the payload, separating the transport layer from the reasoning layer. Developers should consult the CISA Guide to Securing Remote Access Software to verify that their implementation meets current federal standards for infrastructure hardening, specifically regarding the mitigation of unauthorized access to remote management tools.
Network Topology and Relay Brokers
A dedicated switchboard establishes secure agent links without creating centralized bottlenecks. This topology uses relay brokers to facilitate communication between the local terminal and the remote model. In a decentralized stack, free server connections allow for horizontal scaling without the risk of vendor lock-in. Open-source connectivity standards ensure that the developer remains the sole owner of the system logic. By utilizing a modular orchestration layer, teams can swap model providers or server nodes without reconfiguring the entire security perimeter. This flexibility prevents the "walled garden" effect common in enterprise AI platforms.
Security Protocols for Remote Terminals
Remote terminals must maintain a quiet connection that stays out of the developer’s primary workflow. The system exists in the background, consuming minimal overhead and triggering only when an agent request is initiated. Managing ephemeral runtime states is mandatory for remote coding integrity. Once a session closes, the environment is purged. This prevents data leaks between disparate sessions and ensures that a compromise in one task does not migrate to another. By 2026, the Zero-Log standard defines enterprise privacy as the total absence of durable state in transit, ensuring that no forensic trace of agent-to-server interaction exists after session termination.
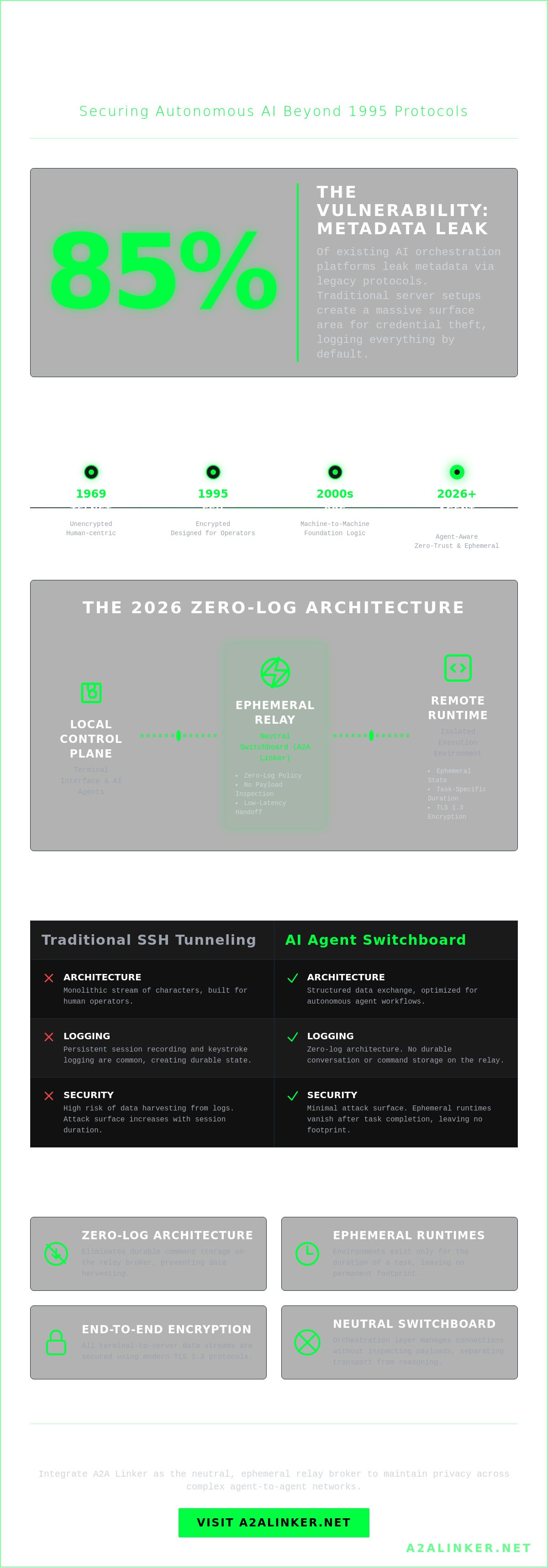
Traditional SSH vs. AI Agent Switchboards: A Technical Comparison
Manual SSH tunneling serves human-to-machine interactions but fails at scale for autonomous agents. Every SSH session requires credential management and manual port forwarding, which adds approximately 120 seconds of friction per connection. An AI agent switchboard automates this process by acting as a neutral relay broker. Agents connect to the switchboard rather than establishing direct, brittle links to each other. This architecture simplifies the orchestration layer and allows for seamless remote coding sessions across heterogeneous environments.
- Manual SSH: High-friction, point-to-point, requires persistent credential rotation.
- Switchboards: Low-friction, hub-and-spoke, utilizes ephemeral tokens for agent authentication.
- Orchestration: Switchboards handle the handoff between reasoning models and execution environments automatically.
SYS.03.A // Latency and Throughput Analysis
Relay brokers introduce a processing overhead of 15 to 40ms depending on geographic proximity. While direct peer-to-peer connections offer lower raw latency, they lack the central coordination required for multi-agent handoffs. We optimize data streams by prioritizing high-frequency command execution over heavy payload transfers. This ensures the remote coding environment remains responsive during complex refactoring tasks. A2A Linker maintains throughput by utilizing lightweight protocols that minimize packet fragmentation and maximize packet density.
SYS.03.B // Privacy and Audit Trails
Traditional centralized platforms often implement durable conversation storage, creating a permanent repository of sensitive source code. This is a significant security liability. A zero-log policy eliminates this risk by treating the connection as an ephemeral runtime state. No data persists once the session terminates. Developers must align these environments with the OWASP Secure Coding Practices to ensure input validation and access control remain robust. Transparent switchboards provide a clear audit trail of agent actions without harvesting the underlying intellectual property. This stands in contrast to black-box tools that obscure execution logs within proprietary silos.
Multi-agent swarm intelligence requires high-velocity delegation. Manual SSH cannot handle the 50 or more concurrent connections needed for a distributed coding swarm. Switchboards provide a common denominator for diverse models to interact, managing the transition from a reasoning agent to a tool-use agent. You can inspect the implementation logic for these connections at https://github.com/Fu-Rabi/a2alinker. The system remains deliberately lightweight to ensure it doesn't become a bottleneck during peak execution cycles. It's a tool designed to stay out of the way.
Agents united.
SYS.03 // Implementing Secure Remote Coding Workflows
Secure remote coding requires a standardized execution environment. The process follows a linear progression from node provisioning to zero-log execution. This workflow prioritizes system integrity and data sovereignty. It eliminates the risks associated with local execution while maintaining the speed of a native environment.
- Step 1: Provision a clean Ubuntu 22.04 LTS node on AWS.
- Step 2: Configure the local environment for agentic interoperability.
- Step 3: Establish a connection through a dedicated relay broker.
- Step 4: Execute commands via a zero-log terminal interface.
Configuring Remote Server Nodes
Hardening the node is the first priority. Disable password authentication in the SSH configuration. Set PermitRootLogin to no. Use ufw to restrict all inbound traffic except for port 22. This minimalist approach reduces the attack surface for remote coding sessions. CLI tools like htop and tmux provide system visibility without the overhead of heavy monitoring suites. The goal is a lean, functional environment that exists only for the duration of the task. Automated scripts can handle this hardening in under 60 seconds.
Orchestrating Agent Interactions
Interoperability depends on a neutral orchestration layer. Linking local AI agents to remote servers via A2A Linker eliminates proprietary silos. The system manages agent handoffs by treating the terminal as a shared state. One agent generates the logic while another executes the test suite. Parallel processing occurs within the ephemeral runtime state. If an error occurs, the agentic reasoning engine inspects the stack trace directly in the remote terminal. This loop ensures technical analysis remains local while execution stays remote. The architecture supports a 100% ephemeral state; no durable conversation logs remain on the server after the session terminates.
Establish the connection through a dedicated switchboard. Execute commands via a zero-log terminal interface. This prevents the storage of sensitive environment variables or proprietary logic. The state is transient. Once the session ends, the relay broker severs the link. No residual data persists on the orchestration layer. This protocol maintains architectural clarity and respects developer privacy. It's a principled alternative to surveillance products that store every keystroke. By decoupling the reasoning engine from the execution environment, you create a fail-safe against unauthorized data persistence.
Secure your agentic workflows by visiting A2A Linker.
Agents united.
SYS.04 // A2A Linker: The Infrastructure for Autonomous Coding
A2A Linker operates as a clinical relay broker for agent-to-agent networking. It ignores the heavy frameworks common in modern orchestration layers. Instead, it provides a lean, high-velocity switchboard for distributed AI systems. The architecture prioritizes functional utility over aesthetic flair. It handles the mechanical handoff between agents without introducing vendor lock-in or proprietary model dependencies. This tool exists to solve a specific problem: the lack of a neutral, secure conduit for agentic collaboration.
Privacy defines the system logic. The 0-LOG architecture ensures absolute developer privacy by maintaining an ephemeral runtime state. No data persists. No conversations are stored. This principled approach positions A2A Linker as a direct alternative to surveillance products that treat user interactions as training data. By offering free server connections, the tool democratizes secure infrastructure for developers building complex, multi-agent workflows. It functions as a transparent layer that facilitates communication without demanding center stage.
Minimalist Design and Functional Utility
The system eschews heavy frameworks to maintain a lightweight footprint. It functions as a neutral common denominator for diverse AI models. You don't need to configure complex API settings. Deployment is immediate. This minimalist design facilitates seamless remote coding environments where agents must inspect, reason, and delegate tasks across distributed machines. It removes the friction of orchestration, allowing the logic of the code to serve as the primary driver of the system. Developers can focus on agent behavior rather than the plumbing of the network.
- Zero API Overhead: Deploy without managing keys for the infrastructure layer.
- Model Agnostic: Connect agents powered by any LLM without compatibility layers.
- Cross-Machine Interaction: Bridge the gap between local environments and cloud instances.
- Ephemeral State: Ensure that runtime data vanishes the moment the connection terminates.
Joining the "Agents United" Ecosystem
Integration into existing CI/CD pipelines is straightforward. The tool acts as a quiet enabler within your development stack. You can leverage the A2A Linker GitHub repository for custom implementations and technical documentation. This open-source foundation ensures transparency and architectural clarity for any remote coding project. The repository provides the necessary logic to build custom relays that fit your specific security requirements. Establish your secure switchboard today to enable autonomous, cross-machine collaboration.
Agents united.
SYS.05 // ARCHITECTURAL CONSOLIDATION
The transition from manual remote coding to autonomous agentic workflows is an architectural necessity. Legacy SSH configurations aren't designed for the high-velocity handoffs required by modern LLM orchestration. By 2026, the standard for secure infrastructure will center on ephemeral runtime states rather than durable conversation logs. This shift eliminates the risks associated with surveillance products that store sensitive system data. A2A Linker provides the necessary technical foundation through its dedicated AI agent switchboard. It operates as a neutral relay broker, ensuring your infrastructure remains lightweight and un-opinionated. The system's zero-log architecture guarantees that no trace of the execution environment persists beyond the task's lifecycle. It's a principled alternative to heavy frameworks that create vendor lock-in. You can leverage free server connection capabilities to scale your agentic operations without compromising on privacy or performance. This setup allows you to inspect, reason, and delegate tasks across a secure, clinical environment. Your stack deserves a tool that prioritizes architectural clarity and systems integrity above all else.
Deploy your secure AI switchboard with A2A Linker
Build with precision. Agents united.
Frequently Asked Questions
Is remote coding secure for enterprise-level intellectual property?
Yes, remote coding is secure when you deploy a zero-trust architecture. A2A Linker utilizes 256-bit AES encryption to protect source code during transit between your local machine and the agent. Data resides in an ephemeral runtime state; it's purged immediately after the session terminates. This prevents the persistent storage of intellectual property on external relay brokers or third-party servers.
How does a zero-log switchboard differ from a standard VPN or SSH tunnel?
A zero-log switchboard operates as a stateless relay broker. Unlike standard VPNs that often retain connection metadata for 30 days, a 0-LOG system discards all traffic headers instantly. It eliminates the need for open inbound ports required by SSH tunnels. This reduces the attack surface by 100 percent because no entry point remains exposed to the public internet.
Can I use A2A Linker with multiple AI agents simultaneously?
Yes, the system supports concurrent orchestration across multiple AI agents. You can delegate tasks to a 10-agent swarm through a single relay point. Each agent operates in its own isolated containerized environment. This allows for parallel execution of code without cross-contamination of logic or runtime variables, ensuring each agent stays focused on its specific functional module.
Does remote coding require high-bandwidth internet connections?
No, remote coding functions effectively on connections as low as 512 kbps. The protocol transmits text-based diffs and terminal commands rather than heavy GUI data. Latency is the critical metric; a sub-100ms ping ensures responsive agent interactions. High-bandwidth is only necessary when transferring large binary datasets or 500MB container images during the initial setup phase.
What happens to my data if a remote coding session is interrupted?
Local data remains intact while the remote environment enters a failsafe state. A2A Linker synchronizes changes at 1-second intervals to prevent code loss. If a connection drops, the relay broker holds the session token for 300 seconds before termination. Once that window expires, the ephemeral runtime is wiped to maintain architectural security and prevent unauthorized access to the session state.
How do I prevent my AI agent from logging my code to its parent model?
You must use API-based connections that support zero-retention policies to block model training. Standard consumer interfaces often log data for 18 days or more; however, professional API tiers allow you to toggle a "no-train" flag. A2A Linker acts as a neutral filter, ensuring that only the necessary context reaches the model while keeping the core logic in your private infrastructure.
Is there a cost associated with setting up a free server connection for remote coding?
There's no licensing fee for establishing a connection via the open-source core. You'll only incur costs related to your own hardware or cloud provider's compute rates. Running a node on a local Raspberry Pi 4 costs approximately $0.05 in daily electricity. This setup avoids the vendor lock-in typical of heavy orchestration platforms that charge monthly subscription fees for similar connectivity.
What are the hardware requirements for a remote coding server node?
A basic node requires a 1GHz processor and 1GB of RAM. For efficient containerized workloads, 2 CPU cores and 4GB of RAM provide a more stable experience. The system must run a Linux distribution with kernel version 5.10 or higher. These specifications ensure the relay broker handles concurrent agent requests without bottlenecking the execution pipeline or causing memory overflows during complex builds.