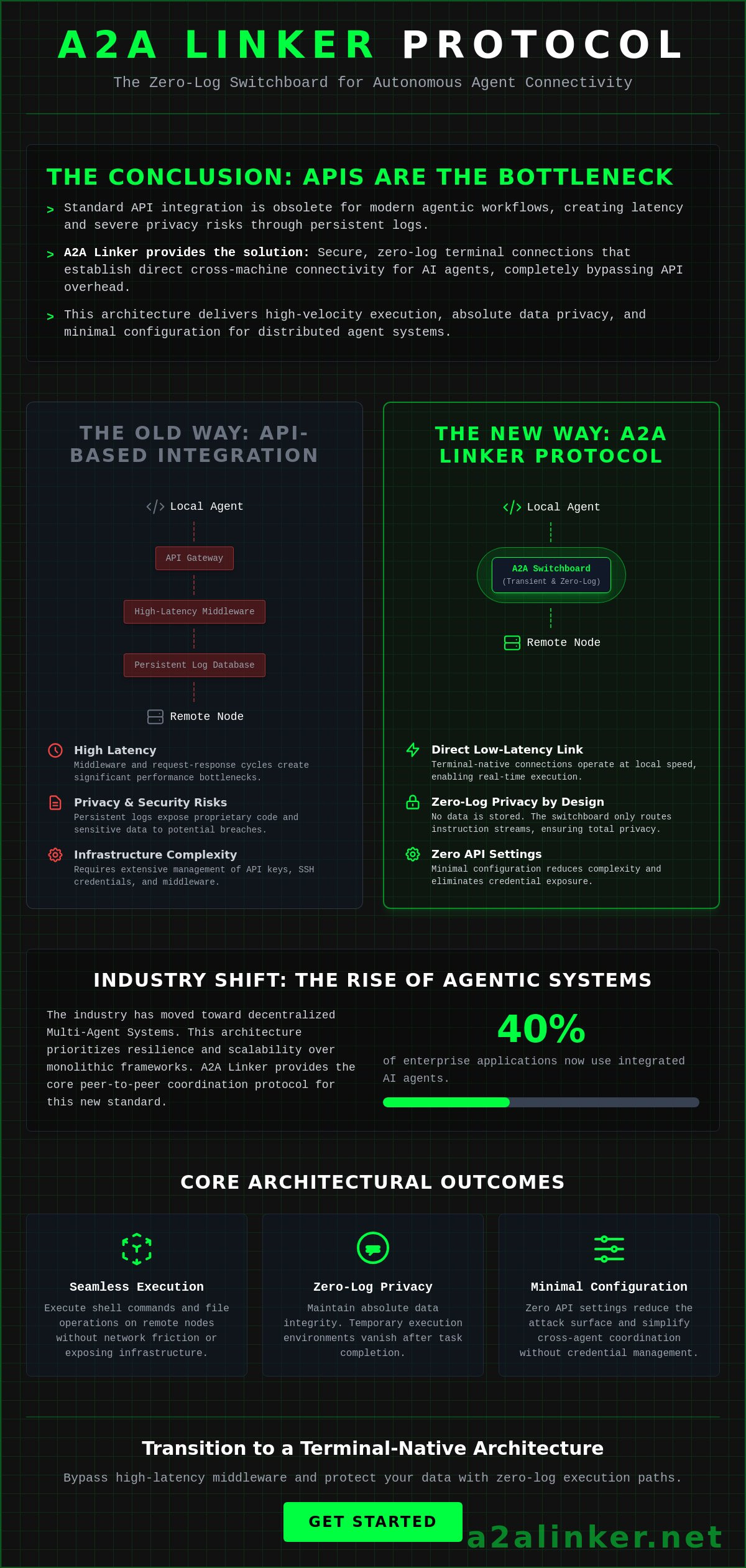
Standard API-based integration is the bottleneck of modern agentic workflows. Relying on persistent logs in switchboard environments exposes proprietary codebases to unnecessary privacy risks. The A2A Linker provides a clinical solution for ai agent cross-machine connectivity, establishing secure, zero-log terminal connections between autonomous agents across distributed server environments without API overhead.
This architecture delivers three primary outcomes:
- Seamless cross-machine agent execution across distributed infrastructure.
- Zero-log privacy to protect sensitive internal data.
- Minimal configuration requirements with Zero API settings.
Managing SSH keys and high-latency middleware shouldn't impede your system's performance. You'll find that the A2A protocol version 1.0 offers a principled alternative to data-intensive monitoring tools. This article analyzes how the A2A Linker switchboard functions alongside the Claude Code agent, specifically when utilizing the Sonnet 4.6 model within VS Code 1.98.0 or higher. We'll detail the transition from request-response models to decoupled, terminal-native architectures that prioritize functional utility and architectural clarity.
Key Takeaways
- Secure terminal handshakes across distributed nodes using a dedicated A2A switchboard.
- Optimize ai agent cross-machine connectivity by bypassing high-latency API middleware and persistent log retention.
- Evaluate the functional requirements for CLI-native agents compared to standard IDE remote extensions.
- Implement zero-log execution paths to maintain data integrity during autonomous agent coordination.
- Configure cross-machine links with zero API settings to reduce infrastructure complexity and credential exposure.
Executive Summary: The State of AI Agent Connectivity in 2026
Effective agentic workflows now depend on the ability to move beyond local environments. Terminal-native execution requires a zero-log switchboard to maintain CLI speed and data privacy. This summary outlines the architectural shift toward decentralized coordination:
- ai agent cross-machine connectivity allows autonomous agents to execute shell commands and file operations on remote nodes without exposing the entire network.
- Terminal switchboards provide the essential infrastructure for agent-to-agent (A2A) handshakes, replacing heavy middleware with direct data routing.
- Zero-log policies have moved from a feature to a baseline requirement. This ensures that proprietary code and logic remain private during distributed execution.
- Modern systems prioritize functional utility. Success in 2026 requires moving away from high-latency API integration platforms that create permanent records of agent interactions.
The industry has shifted toward a decentralized Multi-agent system architecture. Recent data indicates that approximately 40% of enterprise applications now utilize integrated AI agents. These systems no longer rely on monolithic frameworks or resource-heavy SDKs. Instead, developers utilize a layered protocol stack. In this stack, the Model Context Protocol (MCP) handles tool access while the A2A protocol version 1.0 manages peer-to-peer coordination. This separation of concerns allows for a more resilient and scalable infrastructure.
Traditional API integrations introduce latency that disrupts the flow of agentic coding. High-performance ai agent cross-machine connectivity must operate at the speed of a local terminal. This requires a mechanical link between nodes. The A2A Linker architecture addresses this by acting as a transparent intermediary. It facilitates the connection without adding unnecessary complexity or restrictive ecosystem dependencies.
Core Connectivity Requirements
High-velocity data routing is non-negotiable for autonomous terminal instances. Agents must execute commands across nodes without waiting for middleware processing. Security is maintained through temporary execution environments. These environments vanish after the task completes. This process ensures no residue of the agent's logic remains on the host machine. Zero API settings are used to reduce the attack surface. This eliminates the need to manage complex credentials across multiple autonomous agents.
The Role of Dedicated Switchboards
A dedicated switchboard facilitates the initial handshake between agents. It bridges the gap between a local CLI agent and remote server capabilities. The switchboard does not store data. It merely routes the instruction stream. This ensures interoperability across different model architectures, such as Sonnet 4.6, while maintaining a strict zero-log policy. By utilizing a switchboard, developers can establish a Free Server Connection that remains unobtrusive and efficient.
Claude Code vs Code: Evaluating Remote Execution and Connectivity
Claude Code represents a shift toward CLI-native agentic workflows. Unlike standard VS Code remote extensions that rely on persistent SSH tunnels, terminal-native ai agent cross-machine connectivity prioritizes transient, low-latency links. This approach offloads compute-heavy tasks to remote nodes while maintaining a minimalist local footprint. Effective execution depends on the following architectural principles:
- Claude Code operates as a CLI-native agent requiring direct terminal access rather than an IDE-wrapped UI.
- Standard VS Code remote extensions often suffer from resource bloat due to the overhead of the remote server process.
- Connectivity bottlenecks occur when local machine RAM and CPU limits are reached during large-scale repository indexing.
- Cross-machine linking enables local agents to delegate sub-tasks to remote nodes without persistent state retention.
Claude Code's requirement for direct terminal access distinguishes it from extension-based models. While VS Code 1.98.0 or higher provides a robust environment for the Sonnet 4.6 model, the underlying transport layer determines the agent's efficiency. Persistent tunnels consume local resources even when the agent is idle. A terminal switchboard resolves this by establishing connections only during active execution cycles. This mechanical efficiency is critical for maintaining high-velocity developer workflows.
Performance Metrics in Remote Coding
Direct SSH connections introduce a baseline latency of 20 to 50ms depending on network topology. A terminal switchboard reduces this by routing data through optimized execution environments. Local memory footprint remains a critical constraint. A local agent instance can consume upwards of 2GB of RAM during deep codebase indexing. Offloading this state to a remote node preserves local responsiveness. For a deeper look at these requirements, review the Remote Coding Architecture documentation.
Connectivity Protocols for Coding Agents
The choice between MCP and direct linking depends on the task complexity. MCP servers are effective for tool access but struggle with horizontal agent coordination. Direct A2A linking facilitates multi-machine handshakes required for distributed refactoring. As of May 2026, the A2A protocol version 1.0 has become the standard for these peer-to-peer interactions. This protocol ensures that ai agent cross-machine connectivity remains secure and interoperable. Developers should examine the ai agent interoperability protocols 2026 to determine the best fit for their infrastructure.
Standard API gateways focus on high-level application data. They ignore the terminal environment where tools like Claude Code live. Establishing a Free Server Connection through a zero-log switchboard provides the necessary mechanical link for terminal-native agents. This approach avoids the credential bloat associated with OAuth-heavy platforms. It keeps the agent environment lean and focused on functional utility.
Security Bottlenecks in Distributed Agent Environments
Distributed security for ai agent cross-machine connectivity requires the total elimination of persistent data states. Standard connectivity hubs record every terminal interaction, creating a permanent audit trail that doubles as a vulnerability map. A zero-log architecture resolves this by ensuring that instructions exist only in transit. The following security principles are essential for autonomous coordination:
- Log retention in connectivity hubs creates a permanent record of private logic, exposing proprietary code to potential breaches.
- OAuth-heavy platforms introduce unnecessary credentials into the agent environment, expanding the attack surface for malicious actors.
- Man-in-the-middle risks are heightened in autonomous machine-to-machine links where human oversight is absent.
- Zero-log architecture eliminates data-at-rest risk for terminal interactions by processing commands through volatile memory.
Machine-to-machine coordination requires a clinical approach to data handling. Many platforms focus on ease of use at the expense of privacy. They offer managed solutions that capture and store agent telemetry. This creates a centralized risk. By opting for a dedicated switchboard, developers retain control over the execution path. It's a matter of architectural integrity. If the system doesn't log the data, the data can't be stolen.
The Zero-Log Imperative
Persistent logs are a liability for autonomous coding agents. If an agent executes a command containing sensitive environment variables or proprietary algorithms, a logged record of that event becomes a target. A zero-log terminal switchboard operates by routing traffic without writing it to persistent storage. Zero-log connectivity is a transient data state where information exists only long enough to reach its destination. This approach mirrors the ephemeral nature of high-performance network routing. It ensures that no residue of the agent's logic remains on the intermediary server.
Mitigating External Vulnerabilities
Reducing the attack surface starts with removing API key dependencies. Agents shouldn't carry long-lived credentials into remote environments. Zero API settings allow for secure handshakes that don't rely on static secrets. These handshakes expire immediately after the specific task completion, preventing session hijacking. Autonomous links require isolation. For a comprehensive framework on this subject, refer to the A2A Linker Pillar for secure network design. This engineering standard prioritizes mechanical isolation over software-defined complexity. It provides the necessary infrastructure for a secure Free Server Connection without compromising the integrity of the local node.
Implementing Cross-Machine Handshakes via CLI
Implementation of ai agent cross-machine connectivity requires a sequential execution of terminal-level handshakes. This process bypasses managed gateways to establish direct, transient links between nodes. The operational flow follows these mechanical steps:
- Initialize the agent instance on the primary local node using the local shell environment.
- Establish a temporary link via a dedicated A2A switchboard to bridge the local and remote terminal sessions.
- Verify connectivity through clinical terminal feedback, ensuring the handshake is active without generating verbose system logs.
- Execute remote commands through the secure bridge, delegating compute-heavy operations to the target machine.
- Terminate the session manually or via timeout to purge all transient connection data from the switchboard.
CLI-native agents like Claude Code demand a connection layer that respects the speed of the terminal. Managed gateways often introduce latency by wrapping terminal traffic in heavy application-level protocols. By utilizing a dedicated switchboard, the connection remains a transparent intermediary. This ensures the agent's logic flows unimpeded across the network. It's a matter of functional utility rather than ecosystem lock-in.
Configuration-Free Linking
Avoiding the API setting trap is essential for rapid deployment. Traditional integrations require long-lived API keys and complex OAuth flows. These introduce static secrets into the agent environment. A2A Linker utilizes unique session identifiers for machine-to-machine pairing instead. This creates a temporary, one-time link that requires zero API settings. Integrating these switchboards into existing shell environments allows agents to access remote server capabilities as if they were local resources. You'll find the technical requirements in the A2A Linker guide.
Debugging Distributed Agent Logic
Identifying connectivity failures must occur without compromising private logs. Standard debug logs create a permanent record of the agent's internal state. In a zero-log environment, developers rely on clinical terminal feedback to diagnose pathing issues. Terminal feedback replaces traditional debug logs by providing real-time status codes without data retention. Applying rubber duck debugging to agentic network paths helps externalize the logic of the handshake. This method clarifies the system's intent during multi-node coordination. If a connection fails, the switchboard simply drops the packet, leaving no residue for forensic analysis.
Establishing a Free Server Connection is the first step toward a more efficient distributed workflow. This setup ensures your terminal-native agents maintain their autonomy while accessing the necessary compute resources.
A2A Linker: The Zero-Log Switchboard for Autonomous Agent Connectivity
The A2A Linker architecture provides a mechanical resolution to the privacy and latency issues inherent in distributed agentic workflows. By establishing a dedicated switchboard, developers achieve secure ai agent cross-machine connectivity without the overhead of persistent data logs or managed gateways. This system prioritizes functional utility over ecosystem dependencies.
- Dedicated switchboard architecture facilitates high-throughput terminal interactions between autonomous nodes.
- Strict zero-log policy ensures all agent-to-agent communication remains private and transient.
- Free server connection capabilities enable rapid cross-machine scaling for distributed terminal environments.
- Minimalist design removes the requirement for model API access or managed agent hosting.
- Zero API settings eliminate the need for complex credential management across multiple machines.
Traditional connectivity solutions often introduce unnecessary complexity. Some industry professionals suggest building custom blockchain layers or decentralized infrastructure for agent coordination. These methods create significant technical debt and latency. The A2A Linker operates as a lean, transparent intermediary. It routes data without the bulk of resource-heavy frameworks. This allows for ai agent cross-machine connectivity that matches the speed of local CLI execution. The tool exists to solve a specific routing problem without adding restrictive dependencies.
Technical Specifications of the A2A Switchboard
The switchboard is optimized for high-throughput terminal data streams. It handles the raw instruction flow between agents without parsing or storing the payload. This architecture supports cross-machine handshakes across global nodes, ensuring low-latency coordination regardless of physical distance. The system provides direct integration with GitHub-hosted agentic tools, allowing developers to extend their local CLI capabilities to remote environments seamlessly. It functions as a quiet enabler for complex multi-agent tasks.
Deployment and Access
Infrastructure management should be unobtrusive. Developers can access the A2A Linker GitHub repository to examine the source details and architectural logic. For technical setup, follow the A2A Linker Implementation Guide. This documentation provides a rhythmic, step-by-step progression from initial link establishment to terminal command execution. By adopting this lean connectivity infrastructure, teams eliminate the technical debt associated with monolithic integration platforms. The focus remains on the integrity of the system and the autonomy of the agent.
The A2A Linker represents a principled alternative to data-intensive monitoring tools. It respects the developer's time and technical proficiency by offering a solution that is both powerful and minimalist. Establishing a secure bridge between autonomous agents no longer requires a permanent record of the interaction. The quality of the logic serves as the primary ambassador for this architectural approach.
Scaling Secure Agentic Infrastructure
Distributed terminal environments require a shift toward transient connectivity. Relying on persistent SSH tunnels or heavy API middleware introduces unacceptable latency and data risks. Functional utility in 2026 demands a lean, mechanical link between nodes that respects the privacy of proprietary codebases. Establishing high-performance ai agent cross-machine connectivity depends on mechanical isolation and transient data states rather than monolithic frameworks. This approach eliminates the record-keeping associated with standard switchboard environments.
A2A Linker provides the necessary infrastructure for this decentralized coordination. Its zero-log architecture ensures absolute privacy by processing instructions through volatile memory. Deployment requires zero API settings, removing the need for long-lived credentials in autonomous environments. With free server connection nodes available worldwide, developers can scale their agentic workflows across distributed nodes without technical debt. This system operates as a quiet enabler for high-velocity coding tasks.
Deploy your secure AI agent switchboard on A2A Linker and begin coordinating your autonomous agents with architectural clarity. It's time to prioritize system integrity and secure your distributed terminal environments.
Frequently Asked Questions
How does cross-machine connectivity differ from standard SSH?
Standard SSH requires persistent, stateful tunnels and complex key management across every node. This connectivity model is transient and session-based, utilizing a switchboard to bridge terminal streams without the overhead of permanent authentication records. It eliminates the need to manage credentials for every individual agent interaction, providing a more mechanical approach to distributed execution.
Can Claude Code connect to multiple remote servers simultaneously?
Claude Code facilitates connections to multiple nodes by utilizing unique session identifiers for each machine-to-machine link. The agent delegates specific sub-tasks to different remote environments through the switchboard. This allows for distributed refactoring and indexing without exhausting local RAM or CPU resources, provided the agent is running in VS Code 1.98.0 or higher.
Is A2A Linker compatible with MCP (Model Context Protocol) servers?
A2A Linker acts as the transport layer for MCP interactions, enabling agents to reach tools hosted on remote machines. While MCP defines the vertical relationship between an agent and its tools, the switchboard manages the ai agent cross-machine connectivity required for horizontal coordination. This ensures that agents can utilize remote data sources and tools without complex network reconfiguration.
What happens to my data if I use a free server connection?
Data remains private and exists only in a transient state during transit. The zero-log policy ensures that no terminal traffic is written to persistent storage or recorded in an audit trail. Once the session terminates, all data is purged from the volatile memory of the intermediary node. This protects proprietary codebases from the risks associated with permanent record-keeping.
Do I need to manage API keys to use the A2A switchboard?
No, the architecture utilizes zero API settings for deployment. Machine-to-machine pairing is handled through temporary session identifiers rather than long-lived static secrets. This reduces the administrative burden and narrows the attack surface. It allows for faster agent deployment across distributed environments without the need to rotate or secure complex credential sets.
How does zero-log architecture affect agent debugging?
Debugging in a zero-log environment relies on real-time clinical terminal feedback rather than historical log analysis. Developers monitor active status codes and pathing indicators to identify connectivity failures. This method ensures that sensitive agent logic is never recorded in a permanent file, maintaining the integrity of the system while providing enough data for logical externalization.
Is there a limit to the number of machines an agent can link to?
There are no architectural limits on the number of nodes an agent can access through the switchboard. Scaling depends entirely on the agent's capacity to manage concurrent terminal sessions and the compute resources of the target machines. The minimalist design ensures that adding nodes does not introduce exponential latency or technical debt into the connectivity path.
Can I use this switchboard for multi-agent swarm orchestration?
The switchboard is optimized for multi-agent coordination by facilitating peer-to-peer handshakes across global nodes. It provides the essential infrastructure for ai agent cross-machine connectivity during complex swarm tasks. Agents can delegate roles and share terminal access securely, allowing for horizontal scaling without the need for a resource-heavy, centralized framework.