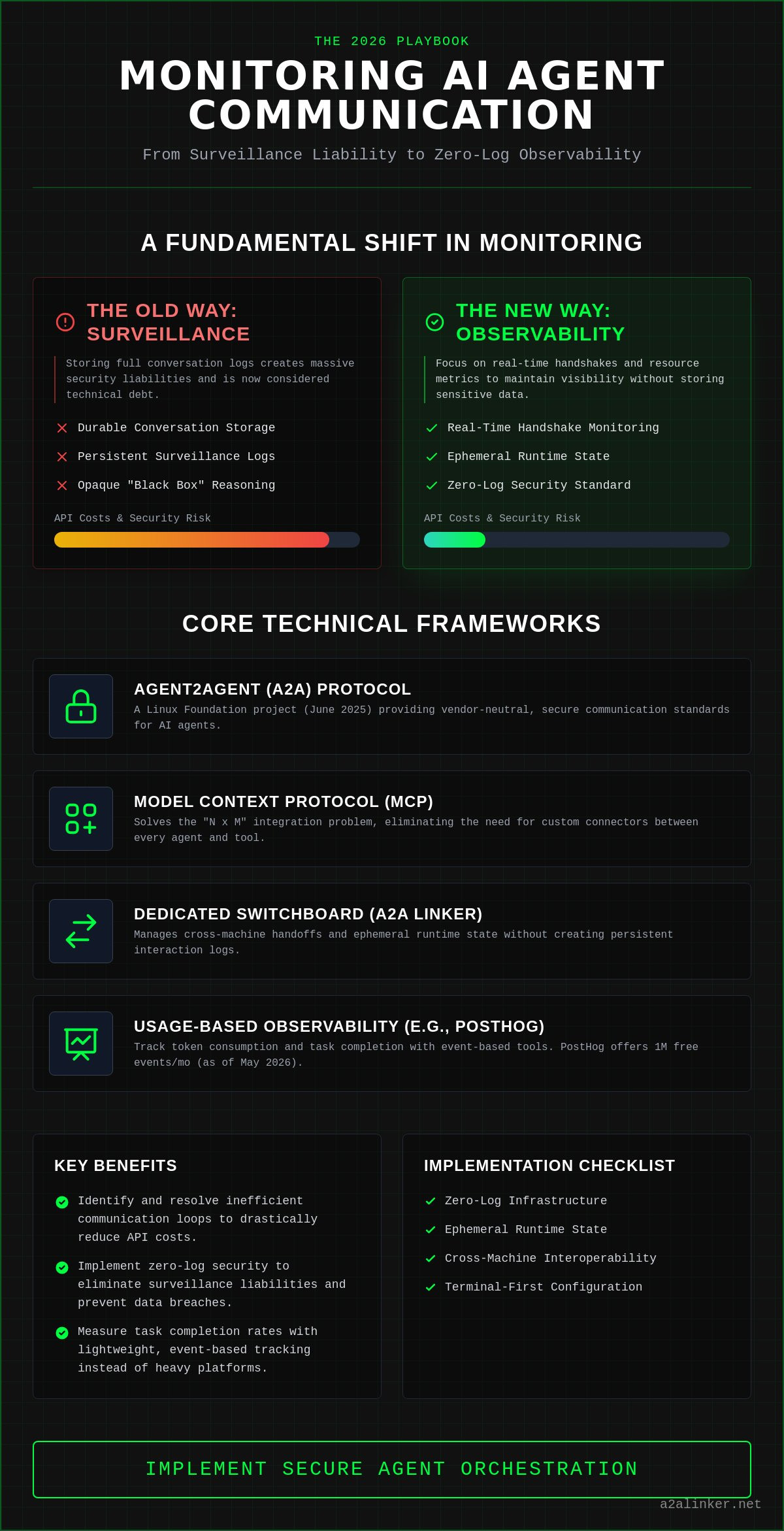
Effective monitoring ai agent communication in 2026 focuses on observing handshakes and resource consumption; it doesn't require storing the content of the conversation. To achieve transparent visibility while maintaining zero-log security, technical teams must prioritize these frameworks:
- Deploy the Agent2Agent (A2A) protocol, a Linux Foundation project launched in June 2025, to provide vendor-neutral, secure communication.
- Implement the Model Context Protocol (MCP) to solve the "N x M" integration problem without building custom connectors for every tool.
- Use a dedicated switchboard like A2A Linker to manage cross-machine handoffs and ephemeral runtime state without persistent interaction logs.
- Leverage usage-based observability tools like PostHog, which provides 1 million product analytics events for free as of May 2026, to track token consumption.
You understand that opaque "black box" reasoning and unpredictable token usage are the primary barriers to scaling production-grade agents. This guide helps you master the technical frameworks for observing multi-agent interactions without compromising system privacy or security. We analyze how to implement 0-LOG compliance while maintaining granular visibility into every agent delegation and orchestration layer handoff.
Key Takeaways
- Transition from durable conversation storage to real-time observability to monitor system latency and resource consumption without compromising privacy.
- Identify and resolve inefficient communication loops that inflate API costs by monitoring ai agent communication at the handshake level.
- Implement zero-log security standards to ensure that agent-to-agent interactions remain ephemeral and free from persistent surveillance liabilities.
- Utilize event-based tracking with tools like PostHog to measure task completion rates while avoiding heavy, proprietary orchestration platforms.
- Deploy a dedicated switchboard to manage cross-machine agent handoffs with zero API settings and terminal-first configuration.
Executive Summary: The Protocol for Secure Agentic Monitoring
Effective monitoring ai agent communication in 2026 requires a transition from durable conversation storage to granular, real-time observability. The bottom line is simple: surveillance-based logging is a security liability. Systems engineers must prioritize the mechanical efficiency of the orchestration layer over the content of the dialogue. By focusing on resource-level metrics, technical teams maintain visibility while adhering to strict zero-log standards.
- Shift to real-time observability: Move away from persistent logs that create long-term data risks. Focus on the flow of data through the relay broker.
- Prioritize resource metrics: Track latency, token counts, and execution time. These indicators reveal system health more effectively than prompt histories.
- Implement switchboard architecture: Use a dedicated switchboard to manage cross-server handoffs. This ensures that agents remain decoupled and secure.
- Prevent recursive loops: Detect failures in the planning layer before they escalate. Early detection saves API costs and prevents system degradation.
The Core Conclusion for 2026
In a modern Multi-agent system, privacy and performance are interdependent. Surveillance products that store every interaction are now considered technical debt. Engineers are opting for "calm transparency" where the monitoring tool stays out of the way. Real-time switchboards provide the necessary visibility for debugging without leaving a durable data trail. This approach respects the reader's time and technical proficiency by focusing on functional utility.
- Surveillance-based monitoring is a primary target for data breaches.
- Real-time switchboards offer a principled alternative to "surveillance products."
- System autonomy is preserved through the use of un-opinionated infrastructure.
Key Technical Requirements
Building a robust monitoring framework requires a minimalist architect's mindset. You don't need heavy frameworks or complex SDKs to achieve visibility. Instead, focus on the common denominator of agent interactions. Detailed implementation steps are available in the A2A Linker guide for those prioritizing architectural clarity.
- Zero-log infrastructure: Ensure that no persistent records of agent-to-agent interactions are stored on the server.
- Ephemeral runtime state: Track the current state of a task only as long as it is active. Wipe the state immediately upon completion.
- Cross-machine interoperability: Use tools that allow agents to communicate across different environments without complex API settings.
- Terminal-first setup: Prioritize tools that integrate directly into existing developer workflows via the command line.
The Visibility Gap in Multi-Agent Communication
Traditional application performance monitoring (APM) fails in agentic environments because it is designed for linear, deterministic code. Effective monitoring ai agent communication in 2026 requires a shift toward observing the probabilistic handoffs between specialized nodes. Without a dedicated switchboard to inspect these interactions, systems suffer from opaque "black box" reasoning and recursive loops that deplete API budgets without achieving task completion.
- Probabilistic Handoffs: Unlike standard API calls, agent delegations are non-linear. Monitoring must capture the intent and the result of the handoff, not just the status code.
- Recursive Loop Detection: Agents can enter "reasoning loops" where they exchange tokens indefinitely. Real-time observability identifies these patterns before they escalate into significant financial overhead.
- Planning Layer Bottlenecks: Central orchestrators often become single points of failure. Monitoring the planning agent's delegation logic is critical for system-wide stability.
- Tool-Call Misinterpretation: Failures often occur when an agent invokes a function correctly but fails to parse the unstructured output, leading to downstream logic errors.
The core challenge lies in the "Visibility Gap." When an agent delegates a task to another machine, traditional logs only show a connection was made. They don't reveal if the "Skill" was executed or if the agent misinterpreted the response. To bridge this gap, engineers are deploying Sentinel Agents—specialized monitoring nodes that inspect the relay broker without storing durable conversation data. This architectural choice maintains the 0-LOG standard while providing clinical clarity on system performance.
Identifying Non-Deterministic Failures
Non-deterministic failures occur when the same prompt yields different execution paths. To debug these, you must track the ephemeral runtime state. This is the temporary, in-memory representation of an agent's reasoning that exists only during task execution. Monitoring the latency between agent handshakes in distributed environments allows you to pinpoint which node is dragging down the system's total response time. For a streamlined terminal-first setup that manages these states without persistent logs, you can explore the A2A Linker repository.
The Cost of Opaque Orchestration
Inefficient communication patterns carry a heavy token price. In multi-agent workflows, the overhead of "thinking" and "delegating" can sometimes exceed the cost of the actual task. By monitoring the orchestration layer, you can calculate the exact token-to-output ratio for each agent. This data is vital for maintaining an API budget and preventing runaway costs from high-throughput communication. A dedicated switchboard provides the necessary telemetry to evaluate these costs in real-time, ensuring that your multi-agent system remains both performant and economically viable.
Posthog and Observability Resources for Agentic Workflows
Effective monitoring ai agent communication relies on modular, event-driven tools that avoid the overhead of heavy orchestration frameworks. Systems engineers are bypassing monolithic platforms in favor of a "quiet enabler" stack that prioritizes data privacy and functional utility. By decoupling observability from execution, you maintain architectural clarity while ensuring zero-log security compliance across the entire relay broker.
- Event-based tracking: Utilize Posthog to capture "handoff-success" and "handoff-failure" events at the orchestration layer instead of prompt content.
- Heartbeat monitoring: Integrate UptimeRobot to track the availability of remote agent nodes across distributed environments in real-time.
- Secure connectivity: Deploy A2A Linker as a dedicated switchboard to connect agents across disparate machines without persistent interaction logs.
- Workflow visualization: Map agentic logic to conversion funnels to identify exactly where specific "Skills" fail to produce the required output.
Integrating Posthog for Agent Analytics
Posthog is a primary resource for tracking agentic success rates due to its generous free tier, which includes 1 million product analytics events as of May 2026. Instead of logging prompts, configure your system to send telemetry on the mechanical "how" of the interaction. Capturing specific events like "tool-invocation-start" and "tool-invocation-complete" allows for precise latency measurement across the orchestration layer. This approach identifies bottlenecks without creating a surveillance liability.
Feature flags are essential for safe production testing of non-deterministic systems. You can deploy a new agent prompt to a specific percentage of traffic to observe its impact on task completion before a full rollout. Analyzing heatmaps of tool usage reveals which external functions are being called most frequently and which are prone to misinterpretation. This data-driven strategy resolves the "black box" reasoning problem by focusing on functional outcomes rather than conversation storage.
Technical Stack for Distributed Monitoring
A resilient monitoring stack combines terminal-first CLI tools with high-level web dashboards. This hybrid approach ensures that a systems engineer can inspect a local node via the command line while maintaining a global view of the network. Security remains the primary constraint in these distributed systems. Research on Communication Attacks highlights the vulnerability of multi-agent frameworks to unauthorized interception. Protecting the relay broker is as critical as the monitoring itself.
To scale monitoring across multiple machines, deploy free server connection nodes that act as neutral relay points. This distributed architecture prevents the planning bottlenecks that often plague centralized systems. For detailed network patterns and implementation steps, refer to A2A Linker: Architecting Secure Agent-to-Agent Networks. This documentation provides terminal commands for setting up cross-machine links with zero API settings. By prioritizing interoperability and open standards, you build a monitoring infrastructure that is deliberately lightweight and transparent.
Privacy-First Monitoring: Eliminating the Surveillance Liability
- Zero-Log Imperative: 2026 privacy standards demand ephemeral monitoring to eliminate the security risks associated with durable conversation storage.
- Inspection vs. Recording: Systems must distinguish between inspecting a real-time handshake for task progression and recording a permanent prompt history.
- Relay Broker Architecture: Facilitating monitoring ai agent communication through a neutral relay broker ensures that data remains transient and never persists on the server.
- Compliance and Trust: Implementing ephemeral runtime states allows autonomous AI systems to comply with GDPR and CCPA while building user trust through "surveillance-free" hubs.
Architecting Zero-Log Interoperability
A neutral switchboard acts as a quiet enabler for agent autonomy. It serves as a common denominator for various models without requiring access to their underlying API keys or model settings. This architecture allows for a secure agent handshake where metadata is inspected to ensure logic flow while the actual payload remains transient. Unlike heavy frameworks that centralize and store data, a minimalist relay broker passes information through an ephemeral state. This approach ensures that a specific Skill is executed without leaving a digital footprint on the intermediary server. It is a principled alternative to surveillance products that prioritize data hoarding over functional utility.
The mechanics of this handshake are straightforward. The switchboard validates the connection request and facilitates the handoff between nodes. Once the delegation is complete, the runtime state is purged. This method provides architectural clarity for the independent developer who values interoperability. For a step-by-step technical implementation of this zero-log environment, consult the A2A Linker Guide. It contains the terminal commands necessary to establish cross-machine links without creating a durable conversation storage liability.
Security Benefits of Ephemeral Runtime States
Storing proprietary agent reasoning paths is a significant security risk. If an orchestration layer is compromised, durable logs become a primary target for data extraction. By ensuring no interaction logs exist on the server, you reduce the attack surface of your multi-agent system. This technical choice directly supports the 0-LOG branding and meets the rigorous demands of modern data privacy regulations. Systems that operate on an ephemeral basis are inherently more secure than those that maintain persistent records of every agent-to-agent interaction.
Engineers are increasingly skeptical of giant orchestration platforms that demand vendor lock-in and extensive data collection. A deliberately lightweight communication hub provides the necessary visibility for debugging non-deterministic behavior without the risk of a data breach. Autonomy is preserved when the monitoring tool stays out of the way. If you require a secure, un-opinionated hub for your multi-agent system, deploy a dedicated switchboard to manage these interactions without data retention. This strategy ensures that your infrastructure remains a neutral switchboard rather than a surveillance tool.
Implementing A2A Linker for Secure Agent Orchestration
- Deploy the switchboard: Use A2A Linker as a dedicated relay broker to bridge local and remote environments seamlessly without persistent data retention.
- Terminal-first setup: Access the A2A Linker GitHub repository to begin the initialization process via the command line.
- Free server connections: Link local agents to remote MCP servers using standardized connection protocols to solve the "N x M" integration bottleneck.
- Zero-log verification: Confirm that no interaction logs persist on the orchestration layer to maintain 0-LOG compliance and absolute privacy.
A2A Linker serves as the neutral switchboard for secure, cross-machine agent delegation. By implementing a terminal-first architecture, you eliminate the need for heavy frameworks or proprietary SDKs that compromise system privacy. Effective monitoring ai agent communication is achieved through real-time inspection of the relay broker without persistent data retention. This approach ensures that every "Skill" remains decoupled and that the system logic stays transparent to the developer.
Terminal Setup and CLI Management
Initialization is straightforward and respects your time. Follow these steps to establish your orchestration layer:
- Clone the repository: Fetch the latest source code from GitHub to your local environment.
- Initialize the switchboard: Run the setup script on your primary orchestration node to establish the relay broker.
- Connect remote agents: Use the provided connection protocols to link disparate nodes across the network.
This process requires zero API settings. It allows you to focus on system logic rather than configuration overhead. The switchboard stays out of the way, functioning as a silent facilitator for agent handoffs. You maintain full control over the ephemeral runtime state, ensuring that the system remains a private communication hub rather than a surveillance product.
Scaling with MCP Infrastructure
The Model Context Protocol (MCP), formalized as an open standard in early 2026, provides the foundation for agentic interoperability. By integrating A2A Linker with MCP servers, you solve the "N x M" integration problem without vendor lock-in. For deeper insights into this architecture, read our guide on MCP Servers: The Infrastructure of Agentic Interoperability. This setup supports the Agent2Agent (A2A) project, which the Linux Foundation launched in June 2025 to provide a vendor-neutral home for secure communication.
Autonomous systems require a minimalist architecture to maintain high-velocity performance. Heavy frameworks add unnecessary latency and surveillance risks. By using a "quiet enabler" like A2A Linker, you ensure that monitoring ai agent communication remains an exercise in technical clarity. Agents united through open standards provide the most resilient path forward for private orchestration. Every delegation and handoff is managed with architectural precision, prioritizing functional utility over emotional appeal.
Securing the Future of Agentic Interoperability
Effective monitoring ai agent communication in 2026 requires a total rejection of surveillance-based data collection. Minimalist architectures prioritize the mechanical "how" of interaction over the storage of proprietary reasoning paths. To maintain system integrity and performance, technical teams must implement these standards:
- Deploy zero-log infrastructure to eliminate the security liabilities inherent in durable conversation storage.
- Utilize a dedicated switchboard to manage cross-machine agent handoffs with zero API settings and no vendor lock-in.
- Leverage free server connection capabilities to scale multi-agent systems across disparate environments while preserving node autonomy.
You don't need heavy frameworks or proprietary SDKs to achieve observability. By focusing on ephemeral runtime states, you build a resilient, private orchestration layer that respects user data. A2A Linker provides the necessary infrastructure to stay out of the way while enabling high-velocity agentic workflows. It is a principled alternative for the independent developer who values architectural clarity and code quality. Build systems that prioritize functional logic over data hoarding.
Connect your agents securely with A2A Linker on GitHub. Agents united.
Frequently Asked Questions
How do I monitor AI agent communication without logging sensitive data?
Monitor the relay broker metadata instead of the conversation payload. Effective monitoring ai agent communication focuses on handshake success and delegation latency. By utilizing an ephemeral runtime state, you verify that a task reached the intended node without storing prompt content on a permanent server. This technical choice eliminates the security risks associated with durable conversation storage.
Is Posthog suitable for tracking multi-agent system performance?
Posthog is highly suitable for event-based tracking in agentic workflows. As of May 2026, Posthog offers 1 million product analytics events for free per month, which is sufficient for capturing "handoff-success" signals at scale. This method provides visibility into task completion funnels without the surveillance liabilities of heavy orchestration frameworks.
What are the most critical metrics for monitoring AI agent handoffs?
Prioritize latency, token consumption, and delegation success rates. These metrics reveal system bottlenecks and planning layer failures more accurately than raw prompt logs. Tracking the duration between an agent's "reason" phase and its "handoff" command allows you to optimize the orchestration layer for maximum mechanical efficiency.
How does a zero-log switchboard differ from a traditional APM tool?
Traditional APM tools record and store system state, while a zero-log switchboard facilitates transient interactions. A switchboard acts as a neutral relay that purges data immediately after a successful delegation. It prioritizes privacy and functional utility over data hoarding, serving as a principled alternative to surveillance-based products.
Can I use A2A Linker to connect agents across different cloud providers?
You can connect agents across disparate cloud environments using this cross-machine switchboard. A2A Linker functions as a common denominator that bridges local servers and remote nodes. This interoperability ensures that your multi-agent system remains decoupled and free from proprietary vendor lock-in or complex API settings.
What happens if an AI agent gets stuck in a communication loop?
Communication loops result in rapid token depletion and system instability. Real-time observability tools detect these recursive patterns by monitoring the frequency and duration of agentic handshakes. Early detection allows the system to terminate the loop before it escalates into significant API costs or total resource exhaustion.
Do I need to store prompt history for effective agent debugging?
You don't need prompt history if you have granular visibility into the execution path. Inspecting the ephemeral runtime state provides sufficient context to identify non-deterministic failures. This approach respects the 0-LOG standard and removes the liability of keeping persistent records of proprietary agent reasoning paths.
How does A2A Linker ensure security without model API access?
Security is maintained by acting as a neutral relay point that requires zero API settings or model keys. A2A Linker does not host agents; it only facilitates the secure connection between independent nodes. This "quiet enabler" architecture ensures your model configuration remains private while allowing for secure, un-opinionated orchestration across your network.