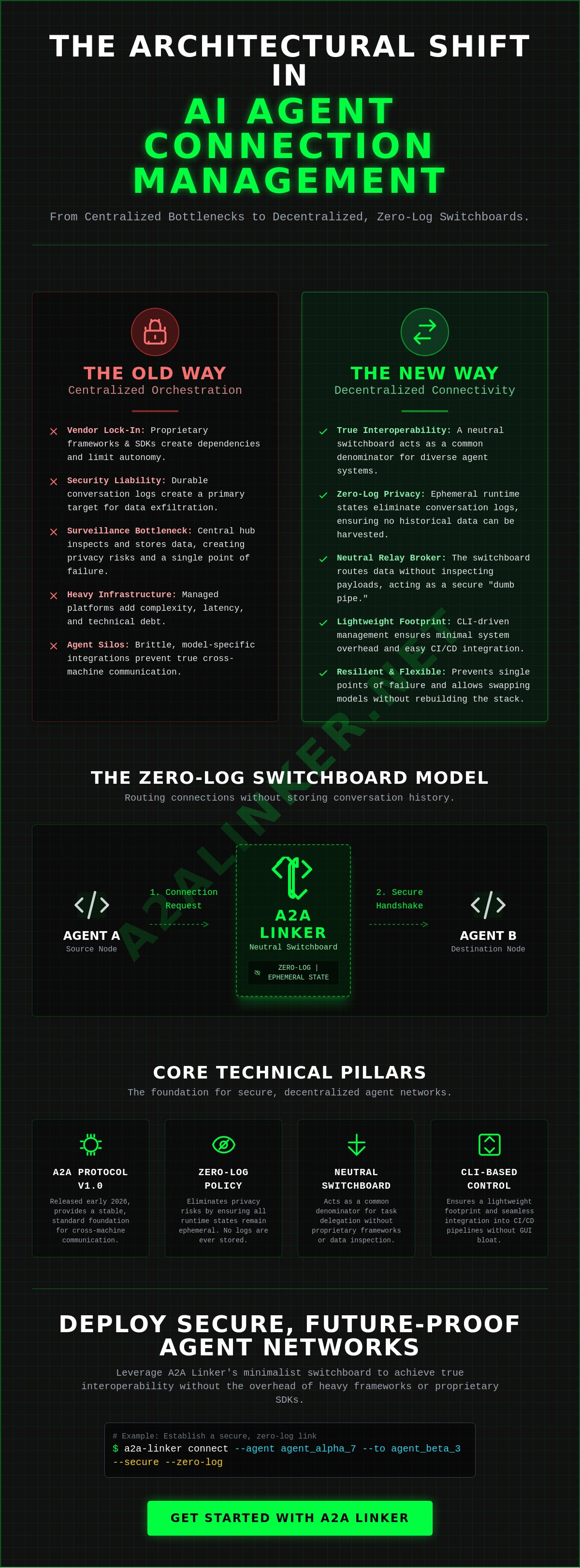
Your current orchestration platform isn't a scaling solution; it's a surveillance bottleneck that forces vendor lock-in. Establishing secure ai agent connection management requires a transition to decentralized, neutral infrastructure. The core technical requirements for this architecture include:
- The A2A Protocol Version 1.0, released in early 2026 by the Linux Foundation, provides the stable foundation for multi-tenant, cross-machine communication.
- Zero-log connectivity eliminates privacy risks by ensuring all runtime states remain ephemeral; no durable conversation logs are stored.
- A2A Linker operates as a neutral switchboard, enabling agents to delegate tasks through a common denominator without proprietary frameworks.
- CLI-based implementations ensure a lightweight system footprint and eliminate the technical debt associated with managed hosting.
You've likely seen how centralized logging turns a simple handoff into a security liability. This technical reference provides the architectural blueprint to master secure A2A networking using zero-log connectivity. We'll examine the mechanics of the A2A Protocol, provide a blueprint for a minimalist switchboard, and outline the terminal commands necessary for a production-ready implementation.
Key Takeaways
- Master the architectural shift from centralized orchestration to decentralized connectivity layers to prevent agent silos and vendor lock-in.
- Implement robust ai agent connection management by utilizing a switchboard model that acts as a neutral relay broker for cross-machine data routing.
- Eliminate privacy vulnerabilities by adopting zero-log protocols that prioritize ephemeral runtime states over durable conversation storage.
- Deploy secure agent-to-agent links across distributed environments using standard terminal commands and remote node configurations.
- Leverage A2A Linker as a minimalist switchboard to achieve true interoperability without the overhead of heavy frameworks or proprietary SDKs.
The Future of AI Agent Connection Management: Core Conclusions
Effective ai agent connection management requires a fundamental shift from heavy, centralized orchestration to a lean, decentralized connectivity layer. Systems that rely on persistent conversation storage create security liabilities and vendor lock-in. It's essential to move toward an architecture that treats the link as a neutral utility. The industry has reached several technical consensus points as of May 2026:
- Decentralization prevents agent silos by allowing cross-machine communication without a single point of failure or a central surveillance node.
- Standardized protocols, such as the A2A Protocol Version 1.0 released in early 2026, abstract model-specific APIs to ensure true interoperability across different environments.
- Security must be architected at the network level using zero-log policies to protect intellectual property during autonomous agentic handoffs.
- Minimalist infrastructure, specifically dedicated switchboards, reduces latency and system complexity compared to heavy, managed hosting platforms.
The modern architecture for an intelligent agent must prioritize privacy and functional utility. By early 2026, over 150 organizations have adopted the A2A standard to facilitate these links. This approach rejects the surveillance model of AI management. It treats agent interactions as ephemeral runtime states rather than durable data assets that can be leaked or exploited. By removing the need for permanent logs, you eliminate the primary target for data exfiltration in agentic swarms.
Executive Summary of Connection Strategies
Architects must prioritize system logic over storage. Reliable ai agent connection management depends on three core strategies to ensure stability and security:
- Prioritize ephemeral runtime states. You shouldn't store conversation logs. This ensures that even if a node is compromised, there's no historical data to harvest.
- Deploy neutral relay brokers. A switchboard should facilitate the handshake between agents on different servers without inspecting or modifying the data payload.
- Utilize CLI-driven management. Terminal-based control allows for granular execution and seamless integration into existing CI/CD pipelines without the bloat of a GUI.
Why Neutrality Matters in Agent Networks
Vendor lock-in remains the primary obstacle to scaling agentic systems. When a platform requires specific model API access, it limits your autonomy and increases operational risk. Neutral switchboards provide a common denominator for diverse autonomous systems. Whether you use custom Python scripts or specialized reasoning engines, the communication layer remains consistent. This separation of the communication layer from the orchestration layer ensures high throughput and architectural flexibility. It allows developers to swap models or frameworks without rebuilding the entire connectivity stack. For detailed implementation steps, refer to the A2A Linker technical guide. By focusing on the mechanical how of agent handoffs, you maintain a flexible, future-proof environment that respects data sovereignty.
Technical Architecture of Agentic Connectivity Infrastructure
Effective ai agent connection management functions as the plumbing of the agentic world. It's the technical process of establishing, securing, and routing data between autonomous systems across heterogeneous environments. While the orchestration layer manages task reasoning, the connectivity layer manages the physical transport. Without a dedicated connectivity layer, developers are forced into brittle, model-specific integrations that fail as soon as the network topology changes. It's the difference between a hard-wired circuit and a dynamic network switch.
The architecture relies on a switchboard model. This relay broker acts as a neutral hub. It doesn't inspect the data payload. It simply routes it to the correct destination node. This design is foundational for robust AI agent security, as it ensures that the infrastructure remains a "dumb pipe" that cannot leak proprietary reasoning logs. By May 2026, terminal-based links have become the standard for cross-machine communication, replacing heavy, centralized platforms with lightweight command-line interfaces that prioritize speed and privacy.
The Dedicated Switchboard Model
A dedicated switchboard enables agents to link across distributed server environments without complex firewall configurations. It simplifies the mechanical process of agent discovery and the initial handshake. Key functional requirements include:
- Discovery: Agents broadcast their availability to the relay broker using the standardized A2A protocol.
- Handshake: Secure authentication occurs via signed agent cards, a feature stabilized in the A2A Protocol Version 1.0 released in early 2026.
- Separation of Concerns: Connection logic stays out of the model's system prompt. This keeps the signal clear and ensures the model's context window remains focused on task execution rather than networking overhead.
If you're building a cross-machine swarm, you should consult a technical guide for node topology to ensure your routing is optimized.
Infrastructure Requirements for Scalability
Scalability isn't just about compute; it's about bandwidth and interoperability. As agent swarms grow, the following requirements become non-negotiable for stable ai agent connection management:
- Bandwidth Management: Relay brokers must handle high-velocity bursts as multiple agents delegate tasks simultaneously across remote servers.
- Free Server Connection Nodes: These nodes lower the entry barrier for independent developers to test distributed swarms without upfront infrastructure costs.
- Interoperability Standards: Use mcp servers, specifically the specification version released on November 25, 2025, to connect agents to internal tools and data sources.
By treating connectivity as a separate utility, you can scale your swarm across any number of remote nodes. You don't need a single, massive orchestration platform when you have a reliable way to link agents united in purpose.
Security Analysis: Zero-Log vs. Logged Architectures
The security of distributed agentic swarms depends on the total elimination of durable conversation logs. Durable storage in ai agent connection management is a liability, not a feature. To maintain system integrity, architects must implement the following security protocols:
- Zero-Log Enforcement: A strict architectural policy where the switchboard stores zero metadata or payloads.
- Ephemeral Runtime States: All interaction data exists only within the temporary execution context of the agents.
- End-to-End Encryption: Traffic must be encrypted at the source and decrypted at the destination, leaving the relay broker blind to the contents.
- Infrastructure Neutrality: Decoupling the communication layer from data-hungry orchestration platforms that function as surveillance products.
Most enterprise platforms fall into the "surveillance product" trap. They claim that logging is necessary for debugging or analytics. However, in high-security environments, these logs represent a massive security deficit. If your switchboard captures payloads, it becomes a single point of failure for your entire intellectual property portfolio. By May 2026, the industry has shifted toward ephemeral states to mitigate these risks. This move ensures that sensitive corporate data remains protected during delegation across remote nodes. You don't need persistent logs to verify that a system is functional; you only need to monitor the health of the connection itself.
Risk Mitigation in Agent Handovers
The delegation phase is the primary attack vector for data exfiltration. When an agent hands off a task, the payload often contains unencrypted reasoning steps or internal database schemas. You must implement end-to-end encryption to protect these transitions. A neutral switchboard acts as a blind relay. It moves packets based on routing headers but cannot inspect the body. This approach reduces the data trail to zero, making it the only logical choice for high-security enterprise environments that cannot afford a breach of their agentic logic. It prevents the infrastructure provider from ever seeing your proprietary data.
Compliance and Privacy Standards
Regulatory frameworks increasingly demand a "Privacy by Design" approach. Achieving this in agentic systems requires zero log architecture to prevent the accidental collection of personally identifiable information. You can still maintain operational oversight without inspecting payloads. Connection management auditing should focus on node-level metrics. Monitor connection duration, packet volume, and node health. These metrics provide sufficient data for system-level integrity checks without infringing on the privacy of the interaction. This method ensures compliance with global standards while keeping your proprietary agentic reasoning private and unrecorded.
Implementing Connection Management via CLI and Remote Nodes
Implementation of ai agent connection management relies on a streamlined, step-by-step technical deployment. This process prioritizes terminal-based efficiency over heavy graphical interfaces or proprietary frameworks. Follow these steps for a production-ready setup:
- Step 1: Configure the remote server environment with secure access protocols, ensuring all nodes are reachable via encrypted tunnels.
- Step 2: Initialize the agent switchboard node using standard terminal commands to minimize system overhead and background processes.
- Step 3: Establish the agentic link via the relay broker address, bypassing the need for manual API key settings or complex orchestration layers.
- Step 4: Verify the handshake using zero-log inspection tools to confirm that no metadata or conversation payloads are being captured by the infrastructure.
- Step 5: Scale the swarm by adding additional cross-machine nodes as task volume and delegation requirements increase.
This modular approach ensures that each connection is a discrete, ephemeral event. By focusing on the command line, you maintain complete control over the routing logic without the interference of a managed hosting provider. It's about building a system that stays out of the way of the agents it connects.
CLI Management for Distributed Nodes
Terminal-based orchestration provides the granularity necessary for complex agentic handshakes. You can automate connection scripts to handle high-throughput swarms, allowing for rapid delegation and task handoffs. Effective ai agent connection management through the CLI means you aren't fighting a bloated framework; you're executing direct system calls that respect the A2A Protocol Version 1.0 specifications. Use modular shell scripts to manage ephemeral states, ensuring that once a task is complete, the connection state is purged from memory. This keeps the system lean and responsive while preventing data leakage. To begin deployment, access the A2A Linker switchboard to initialize your first node.
Secure Remote Access Protocols
Security in a distributed environment begins at the transport layer. You must enable ssh on ubuntu to provide a secure foundation for remote orchestration. Key management is critical here. Use ED25519 keys for the best balance of speed and security across your nodes. For teams utilizing cloud infrastructure, integrating aws marketplace nodes into your connectivity architecture allows you to leverage pre-configured environments while maintaining a neutral switchboard. This setup preserves your autonomy by keeping the communication layer separate from the cloud provider's proprietary AI tools. It ensures your agents remain united across any machine, whether local or remote, without compromising on the zero-log principle that protects your proprietary agentic reasoning.
A2A Linker: The Neutral Switchboard for AI Agents
A2A Linker functions as the architectural resolution to the complexities of distributed agent networking. It provides a neutral, high-velocity switchboard that prioritizes system clarity and data sovereignty. Implementing this tool ensures your ai agent connection management remains robust and private. Key operational benefits include:
- Dedicated Switchboard: A minimalist hub that facilitates secure agent interactions across heterogeneous environments.
- Zero-Log Architecture: A strict non-retention policy ensures that all interactions remain private and unrecorded.
- Free Server Connection: Capabilities that enable seamless cross-machine communication without upfront infrastructure costs.
- Zero API Settings: A design that allows for rapid deployment by eliminating model-specific configuration overhead.
The system operates as a "quiet enabler." It doesn't participate in the reasoning process or store the output of the agents it connects. Instead, it manages the mechanical handoff between nodes. This approach addresses the primary pain points of modern agentic systems: complexity, privacy risk, and vendor lock-in. By treating connectivity as a separate utility, A2A Linker allows developers to build swarms that are truly portable across different cloud providers and local hardware.
Architectural Advantages of A2A Linker
The design is deliberately lightweight. It avoids the bloat associated with heavy frameworks that attempt to manage the entire agent lifecycle. A2A Linker focuses exclusively on the connectivity infrastructure. This specialization ensures high throughput and low latency during agentic delegations. Whether an agent is handing off a specific skill or reasoning step, the switchboard ensures the packet reaches the destination node without inspection. It supports diverse agent skills and cross-environment handoffs, making it a versatile tool for independent developers who value autonomy. By adhering to the A2A Protocol Version 1.0 specifications stabilized in early 2026, it provides a future-proof foundation for any ai agent connection management strategy. It removes the need for proprietary SDKs, favoring open standards and terminal-based control.
Getting Started with Secure Connectivity
Transitioning to a decentralized agent network requires minimal setup. You don't need to manage complex API keys for each individual link. Instead, you initialize your nodes and connect them to the switchboard relay. For detailed, step-by-step instructions on configuring your remote server environment, refer to the A2A Linker technical guide. This documentation covers the terminal commands necessary to establish your first cross-machine link. Developers can also access the open-source repository on GitHub to view the latest community-driven updates and contribute to the core connectivity logic. This collaborative approach ensures the tool remains a neutral, transparent alternative to the surveillance-heavy platforms currently dominating the market. Join the movement toward a more private, interoperable AI future. Agents united.
Establishing Your Decentralized Agent Network
Efficient agentic swarms rely on the total separation of the communication layer from the reasoning layer. By adopting a neutral switchboard architecture, you resolve the primary technical barriers to scaling distributed systems:
- Privacy: Zero-log policies ensure that no metadata or payloads are stored; this eliminates the surveillance risks inherent in managed hosting.
- Interoperability: Standardized A2A protocols allow diverse agents to link across remote servers without proprietary SDKs or framework bloat.
- Autonomy: CLI-based orchestration maintains granular control over ephemeral runtime states and cross-machine handoffs.
Your ai agent connection management strategy should prioritize functional utility over durable storage. The transition to the A2A Protocol Version 1.0, adopted by over 150 organizations as of April 2026, marks the end of the surveillance product era for AI development. You now have the tools to link agents united in purpose while maintaining absolute data sovereignty. Secure your infrastructure by removing the middleman's eyes from your logic.
Deploy your secure agent switchboard with A2A Linker and leverage a strict zero-log privacy policy with free server connection infrastructure. It's time to build a private, interoperable future.
Technical FAQs: Secure Agent Interoperability
What is the primary benefit of a zero-log switchboard for AI agents?
A zero-log switchboard eliminates the security liability of durable conversation storage by ensuring no metadata or payloads are stored on the infrastructure. Traditional surveillance products capture conversation logs, creating a permanent data deficit. By May 2026, high-security enterprise environments have shifted to ephemeral runtime states. This ensures that even if a node is compromised, there's no historical data trail to harvest. Privacy by Design remains the core architectural priority.
How does AI agent connection management differ from standard API management?
Standard API management controls access to static endpoints, while ai agent connection management facilitates the dynamic, ephemeral transport layer between autonomous systems. Standard APIs often require durable keys and persistent sessions. Agentic connectivity focuses on the mechanical how of the handshake and delegation across distributed environments. It abstracts away model-specific logic to provide a neutral common denominator for cross-machine swarms.
Can I connect agents across different cloud providers using A2A Linker?
Yes, A2A Linker functions as a neutral relay broker that facilitates links between agents on any combination of cloud providers or local servers. It provides a free server connection infrastructure that bypasses the vendor lock-in typical of giant orchestration platforms. Whether your nodes are on AWS, Azure, or private hardware, the switchboard ensures a seamless handshake. This cross-machine capability is essential for building resilient, distributed agentic swarms.
What is the role of MCP in agent connection management?
The Model Context Protocol (MCP), specifically the version released on November 25, 2025, handles the connection between an agent and its internal tools or data sources. In contrast, ai agent connection management through the A2A Protocol handles the coordination between different agents. These are complementary standards. Many production systems use MCP for tool access and A2A for agent-to-agent delegation across remote nodes.
Is it possible to manage agent connections via a CLI?
Terminal-based orchestration is the standard method for managing agent nodes and switchboard configurations. Using a CLI allows for granular control and easy automation through shell scripts without the bloat of a GUI. This minimalist approach aligns with the hacker ethos of prioritizing code quality and system logic. It enables developers to initialize nodes, verify handshakes, and scale swarms with high-velocity command-line execution.
Why should I avoid centralized logging in multi-agent systems?
Centralized logging turns your connectivity infrastructure into a surveillance bottleneck and a single point of failure. If an orchestration platform stores every interaction, it becomes a high-value target for attackers seeking proprietary agentic reasoning. Avoiding these logs prevents the accumulation of technical and security debt. Ephemeral states ensure that your intellectual property remains private and is purged immediately after the task delegation is complete.
Does A2A Linker require access to my AI model API keys?
No, A2A Linker operates with zero API settings and never requires access to your AI model API keys. The switchboard acts as a dumb pipe for routing packets between nodes. It doesn't host agents or provide model access. This separation of concerns ensures that your credentials remain secure on your own infrastructure while the switchboard manages only the transport layer.
How do I ensure secure remote access for my agent nodes?
Secure remote access is established by configuring SSH on Ubuntu nodes and using ED25519 keys for authentication. This foundation ensures that all cross-machine traffic is encrypted before it reaches the relay broker. Managing permissions across distributed environments requires a strict policy of least privilege. By combining secure shell access with a zero-log switchboard, you create a hardened environment for autonomous agentic interactions.